Experiencing issues with your Syslog Server not receiving logs from your Palo Alto Networks firewall? This is a common problem network administrators face. Let’s delve into a troubleshooting scenario and explore the configurations and steps to verify connectivity and ensure your logs are being forwarded correctly.
The user in this scenario has configured their Palo Alto Networks (PA) firewall and a dedicated syslog server, but is encountering a problem where no logs are arriving at the syslog server. They have meticulously followed setup guides, but the syslog server, listening on port 5140, remains inactive, showing zero hits even with significant network activity.
Let’s examine the configurations and troubleshooting steps taken to pinpoint the issue.
First, the syslog server is configured to listen on port 5140. This is a non-standard port, as port 514 is typically used for syslog, but using a different port is perfectly acceptable as long as the firewall is configured to send logs to this port.
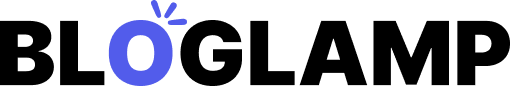
Next, the Palo Alto Networks firewall’s Log Forwarding Profile is configured. This profile dictates which logs are sent to external logging servers. It is crucial to ensure that the appropriate logs (e.g., traffic logs, threat logs) are included in this profile and that the correct syslog server is added as a destination.
 Palo Alto Networks Log Forwarding Profile configuration for sending logs to a syslog server.
Palo Alto Networks Log Forwarding Profile configuration for sending logs to a syslog server.
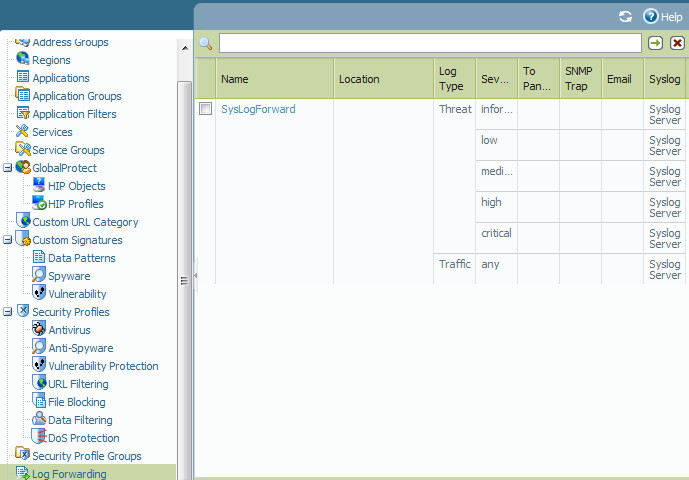
Service Routes on Palo Alto firewalls define the path that management and logging traffic takes. It is essential to verify that the service route for syslog is correctly configured to allow the firewall to reach the syslog server, especially if the syslog server is on a different network segment.
 Palo Alto Networks Service Route configuration for syslog traffic.
Palo Alto Networks Service Route configuration for syslog traffic.
Despite these configurations, a packet capture (tcpdump) on port 5140 revealed no traffic hitting the syslog server, indicating a potential blockage or misconfiguration preventing the logs from being sent.
To further investigate basic connectivity, the user configured the Palo Alto firewall to send system logs to the syslog server. System logs are internal firewall logs related to system events and operations, not user traffic.
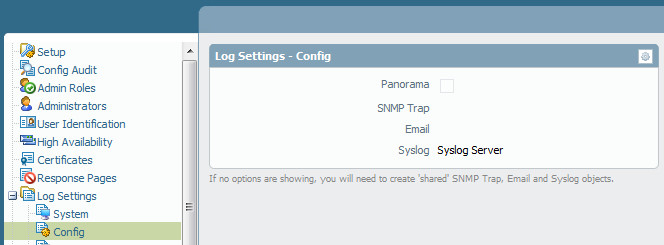 Palo Alto Networks system syslog configuration for internal logs.
Palo Alto Networks system syslog configuration for internal logs.
Interestingly, after configuring system logs, the syslog server started receiving a few hits. This confirms that basic network connectivity between the Palo Alto firewall and the syslog server exists and that the syslog server itself is functioning correctly.
This result suggests that the issue is likely not with the syslog server itself or fundamental network reachability. Instead, the problem might lie within the configuration related to traffic logs forwarding or firewall policies that are not allowing traffic logs to be sent to the syslog server on port 5140.
Possible Troubleshooting Steps:
- Verify Security Rules: Double-check the security rules on the Palo Alto firewall to ensure that traffic logs are indeed being generated and that there are no rules inadvertently blocking the log forwarding process to the syslog server on port 5140.
- Log Forwarding Profile Association: Confirm that the Log Forwarding Profile is correctly attached to the security rules that are processing the traffic you expect to be logged and forwarded.
- Service Route Specificity: While basic connectivity is confirmed with system logs, ensure the service route used for syslog is the correct one and is not restricted in any way that might affect traffic log forwarding specifically.
- Syslog Server Port and Protocol: Double-check that the syslog server is indeed listening on UDP or TCP port 5140, as configured in the Palo Alto firewall. Verify the protocol (UDP or TCP) matches on both sides.
- Firewall Logs (Local): Examine the Palo Alto firewall’s local logs to see if there are any errors or indications that log forwarding is failing. Look for system events related to log forwarding processes.
- Commit Configuration: Ensure that all configuration changes on the Palo Alto firewall have been committed successfully. Inconsistent configurations can lead to unexpected issues.
By systematically reviewing these configurations and potential bottlenecks, you can effectively troubleshoot why your syslog server might not be receiving logs from your Palo Alto Networks firewall and restore proper log forwarding functionality.